

linking INTEGRITYIntegrity - use of values or principles to guide action in the situation at hand.Below are links and discussion related to the values of freedom, hope, trust, privacy, responsibility, safety, and well-being, within business and government situations arising in the areas of security, privacy, technology, corporate governance, sustainability, and CSR. Software Bugs Threaten Toyota Hybrids, 31.8.05
Software Bugs Threaten Toyota Hybrids
Embedded software now controls some of a car's most critical operations, including engine performance, air bags, steering, anti-lock braking systems and stability control systems. If Toyota, which consistently tops vehicle quality surveys, can't get it right, how bad is the rest of the industry? (0) comments Most scientific papers are probably wrong (and I think they should be), 30.8.05
NewScientist.com
Most published scientific research papers are wrong, according to a new analysis. Assuming that the new paper is itself correct, problems with experimental and statistical methods mean that there is less than a 50% chance that the results of any randomly chosen scientific paper are true. John Ioannidis, an epidemiologist at the University of Ioannina School of Medicine in Greece, says that small sample sizes, poor study design, researcher bias, and selective reporting and other problems combine to make most research findings false. But even large, well-designed studies are not always right, meaning that scientists and the public have to be wary of reported findings.
In the paper, Ioannidis does not show that any particular findings are false. Instead, he shows statistically how the many obstacles to getting research findings right combine to make most published research wrong. [...] [CLB: The targeted readership, other researchers, understand this point generally. Publishing reserach results is expected to lead to discussion, further research on the hypothesis, and often refutation, with improved or modified hypotheses emerging. The problem arises from the media and laypersons use of published research. Media is likely to publish startling, 'newsworthy' results to make headlines. They don't include the rest of the scientific process. What's missing in the popular press: repeating the results, relating the results to other findings, systematic analysis and synthesis of the results, and taking sample-based results in a reliable way into an understanding of how these actually relate to the more general population.] (0) comments Concern over Compliance, Instant Messaging and Internal Attacks Spurring Changes, 29.8.05
Business Wire
Regulatory compliance, internal attacks, and the vulnerability of electronic communications - especially instant messaging and e-mail - are among the key factors reshaping data security systems, according to the U.S. results of the 8th annual Global Information Security Survey by InformationWeek Magazine and Accenture. At the same time, the U.S. Information Security Survey uncovered indications that companies and organizations are failing to provide rigorous protection of customer and client data. The survey, which was conducted over the Web this summer, received responses from more than 2,500 U.S. information technology and security professionals. Highlights: "Companies are taking a more structured approach to information security and making it more of a priority," said Alastair MacWillson, partner in charge of Accenture's security practice. "Many companies are beginning to see the benefits in leveraging new technologies to proactively assess and manage threats and vulnerabilities, and are consolidating, integrating and securing applications to improve integrity and productivity." Regulatory Impact
Threat Perception and Attacks Security attacks are constantly evolving, making it difficult for companies to stay one step ahead. For example: Security Tactics As a result of the vulnerabilities with instant messaging and E-mail, electronic communication has become a major focus of employee monitoring with attachments and content of outbound messages carefully scrutinized. Basic-user passwords still remain the most prevalent method used by companies to protect themselves against security breaches. Informing employees of privacy or behavior standards, posting privacy policies online and using secure Web transactions are the steps taken to safeguard the privacy of customer data. In addition, the survey reveals that: Security Costs A majority of U.S. companies spend below $500,000 on security expenses, with half anticipating increased spending in 2005 over the previous year, and only 3 percent expecting spending to decline. Performance and return on investment count the most when purchasing security products. "Despite the fact that information security professionals are adopting many state-of-the-art security practices, certain lapses still exist that can result in serious financial losses for corporations or a violation of customer trust," said Rusty Weston editor, InformationWeek Research. "Security professionals lack the ability to control every point of entry, but worse, they have too much faith in technology that claims to automate network defenses." (0) comments Methods for authentication, 12.8.05
Network World
Passwords don't work very well for crowds. Tokens are used all the time - consider airline tickets and passports - but in today's digital scanning and printing world, they are easy to counterfeit. [... more on advanced ways to make each method work.] (0) comments 'Car Whisperer' puts hackers in the driver's seat, 4.8.05
Computerworld
If your car murmurs 'hello there,' your Bluetooth system has been hijacked
If you happen to hear a disembodied computer voice tell you to 'drive carefully' the next time you're behind the wheel, you've probably met the Car Whisperer.
Released late last week at the What the Hack computer security conference in Liempde, Netherlands, Car Whisperer is software that tricks the hands-free Bluetooth systems installed in some cars into connecting with a Linux computer.
Car Whisperer was developed by a group of European wireless security experts, called the Trifinite Group, as a way of illustrating the shortcomings of some Bluetooth systems, said Martin Herfurt, an independent security consultant based in Salzburg, Austria, and a founder of Trifinite.
The software takes advantage of the fact that many of these hands-free systems require only a very simple four-digit security key -- often a number such as 1234 or 0000 -- in order to grant a device access to the system. Many car manufacturers use the same code for all of their Bluetooth systems, making it easy for Car Whisperer to send and receive audio from the car.
Using a special directional antenna that allowed him to extend the normally short range of his Bluetooth connections to about a mile, Herfurt was able to listen and send audio to about 10 cars over a one-hour period recently.
(0) comments The modern spy..., 1.8.05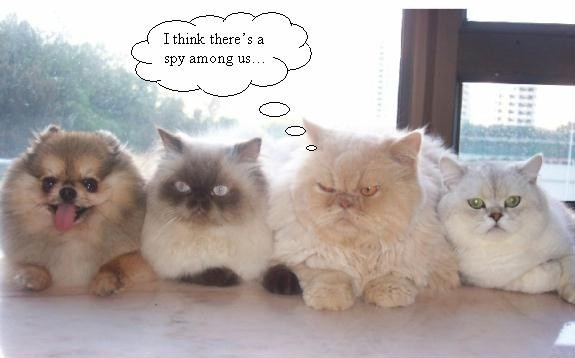 [CLB] Following the news this morning. There are a larger than normal number of 'spy' articles. And the topics are fascinating. We are watching the roll-out of ubiquitous watchware. It's time that each of makes the assumption that every action, every purchasing choice, every movement you make is being monitored somehow. [CLB] Following the news this morning. There are a larger than normal number of 'spy' articles. And the topics are fascinating. We are watching the roll-out of ubiquitous watchware. It's time that each of makes the assumption that every action, every purchasing choice, every movement you make is being monitored somehow.The techniques used rely on technologies that have been around for years. They are being used more systemic to monitor, collect, analysis, and react more effectively. Where was I? MORE: Google Earth Parking Meters In Pacific Grove, Calif., parking meters know when a car pulls out of MORE: THE WALL STREET JOURNAL Colour Printers MORE: The Register What did you wear today? If all these organizations were to share data, they'd know which movie ticket I printed out, how long I parked and where to see theshow, and what I wore. And hopefuly they'd offer some advice about my date, and perhaps even who else he is seeing. How much do you rely on being anonymous in your activities? [CLB] (0) comments
Archives07.03 08.03 09.03 10.03 11.03 12.03 01.04 02.04 03.04 04.04 05.04 06.04 07.04 08.04 09.04 10.04 11.04 12.04 01.05 02.05 03.05 04.05 05.05 06.05 07.05 08.05 09.05 10.05 11.05 12.05 01.06 02.06 03.06 04.06 05.06 06.06 08.06 09.06 10.06 11.06 01.07 02.07 03.07 04.07 07.07 08.07 09.07 10.07 05.08 06.08 | |||||||